Isolated Network Environments
- Lots of malware makes network connections to local and remote machines. Can be instructive to watch this traffic to see what is happening
- e.g. by using tools such as
tcpdumpor WireShark
- e.g. by using tools such as
- However, we do not want the malware to infect other computers or phone home, so we need to be able to run it in an isolated network environment
- Relatively straight-forward to build an isolated LAN.
- But we want to be able to see traffic going to remote machines on the Internet…
- Need to build an isolated 'Internet'…
- Not as hard as it sounds!
- The following assumes that you are building this using virtual machines, but the same principles apply if you want to build it using real hardware (e.g. to watch malware on a phone handset via an isolated wireless network).
- Golden Rule: Check you are isolated before you run anything!
traceroute/pingare your friends here
Isolated Internet Topology
- Aiming for a topology similar to the one shown in the following diagram:
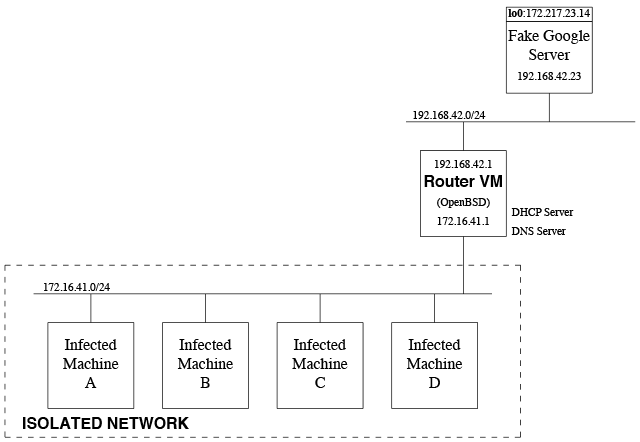
- Technically, only the VMs in the dashed box need to be completely isolated, but I'd advise caution and connect the other bits to the real Internet only when needed
- Three main components of the network
Isolated Network
(represented by the dashed box)
- This is where we run our isolated VMs, important that this network does not connect to the host machine in anyway.
- Notice, I've assigned this an IP range in an RFC1918 space but this is entirely optional — remember this network is not on the Internet so we can use any IP addresses we like :)
- Need to create this as a separate isolated network in the hypervisor. Using VMWare as an example, this is a two step process, which mimics the physical process of setting up a network:
- Create a new network (under Preferences)
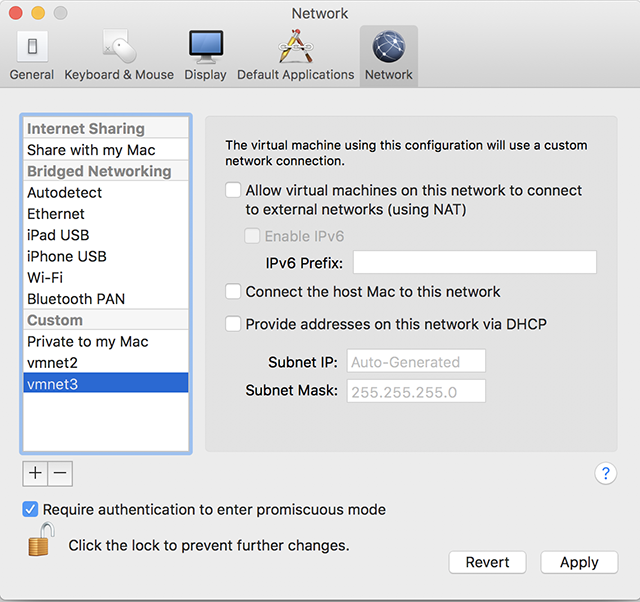
Ensure that all the options are turned off, we do not want the host computer to be able to access this and we'll provide DHCP/DNS via our router - Attach the isolated VMs' NICs to this network alone:
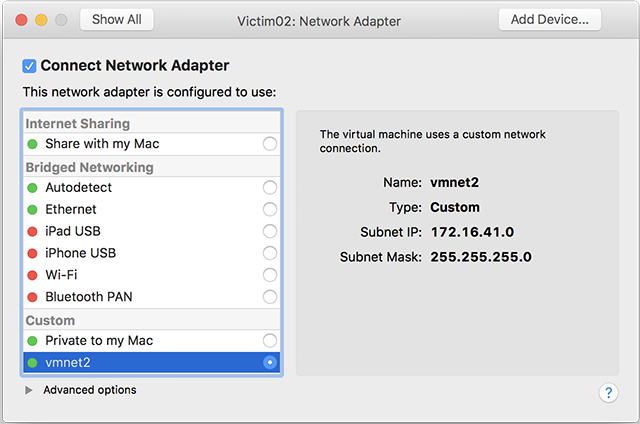
Make sure this is the only NIC in these VMs otherwise they'll be able to talk to the real internet.
- Create a new network (under Preferences)
Router VM
- Routes packets from the isolated network to elsewhere.
- Standard VM, could run Windows, Linux, (Free|Open|Net|Dragonfly)BSD etc. — any OS that can route packets.
You may need to enable packet fowarding withsysctl - My preference here is to use OpenBSD
- Designed to be secure by default!
- Also has some nice networking features (such as allowing multiple virtual routing tables) that can be useful as your setups get more advanced…
- Also
pf, OpenBSD's firewall, is much simpler to configure thaniptablesIMO!
- Will have multiple (virtual) NICs.
- One in the isolated network
- One to connect to the network containing any services being provided to the isolated network
- Note down the MAC addresses of these NICs when creating them — very useful to help find which NIC is which in the router OS.
- Provides DNS/DHCP services to our isolated network
- Need to be able to provide both a recursive DNS server for isolated VMs to use
- DNS server logs will tell us what domains our machines are looking at
- Can be clever and return a honeypot address for all domains queried
- But watch out for malware that checks for this!
- Do you want this to fetch real addresses from the Internet? Interesting question, DNS can be used as a back channel for communication
- And also, an authorative DNS server so we can add/override our own entries.
- Lots of software options here, but I'd probably start with djbdns for DNS…
- Need to be able to provide both a recursive DNS server for isolated VMs to use
- Install WireShark,
tcpdumpetc.
Can be used to sniff traffic leaving the isolated network. Depending on the implementation of the hypervisor, you might be able to sniff all network traffic on the isolated network. - Even if hypervisor doesn't let you sniff all traffic on the isolated network, it is possible to architect your network around this (create an individual isolated network for each VM and bridge together in the router…)
VMs to provide copies of Internet Serviecs
- These are optional, you don't necessarily need them
- Again exist on a separate isolated network in your hypervisor. Create this in the same manner as before
- Again, the diagram shows I've used RFC1918 IP addresses here. Note though that I chose a vastly different set of IPs to make it clear which network is which!
- Probably makes sense to use static IP allocation here, so you know which VM is providing which service
- Can use whatever OS you like
- Setup services as normal, e.g. use Apache WWW server to create a 'Fake Google'…
- Configure DNS server on router to provide the server's IP for any domain (e.g.
www.google.comshould return192.168.42.23for our 'Fake Google' example in the diagram above). - Some machines will attempt to connect directly to a known IP, e.g. to
172.217.23.14(instead ofwww.google.com) - This is relatively straight-forward to cope with
- Set up the desired IP as an alias on the loopback interface of the machine providing the service with a netmask of
255.255.255.255(/32), so for the example in the diagram, we'd create the alias using:- Linux:
ip -4 addr add 172.217.23.14/32 dev lo - OpenBSD:
ifconfig lo0 inet alias 172.217.23.14 netmask 255.255.255.255
- Linux:
- Tell the router to route packets to that IP, to the IP address of the VM providing the service
- OpenBSD:
route add 172.217.23.14/32 192.168.42.23
- OpenBSD:
- Route will now send any packets for
172.217.23.14to the correct VM - Turn on packet forwarding on the VM providing the service, via
sysctl, otherwise the VM won't answer the packets - Same approach will work for SSL/TLS encryped connections, but you'll need to add your signing certificate to the infected VMs.
- Set up the desired IP as an alias on the loopback interface of the machine providing the service with a netmask of
- Will probably end up adding more services as you see what the malware tries to access
- Run them on separate VMs and build up a library of common services to reuse (via VM snapshots/clones).
- Could also allow some packets to access the real Internet, but be careful! (Add another virtual NIC to the router VM that is connected to the Internet)