Ph.D. Dissertation Defense
Fabrication and Operation of Integrated Distributed-Bragg-Reflector
Thermally Tunable Quantum Cascade Lasers
Liwei Cheng
10:00am Friday, 22 June 2012
Center for Advanced Studied in Photonics Research Conference Room
Quantum cascade lasers (QCLs) that emit in the mid-infrared (IR) range between 3 and 10 μm of the electromagnetic spectrum play an important role in optical gas sensing and molecular spectroscopic applications because several important environmental molecules such as CO, CO2, CH4, and NH3 are known to exhibit strong absorption lines in this mid-IR range. To differentiate such fine absorption features as narrow as a few angstroms, a single-mode QCL with an extremely narrow spectral linewidth, broadly tunable over the molecular absorption fingerprints and operating at sufficient optical power at room temperature, is highly desirable. We present, in this dissertation, two major studies on mid-IR QCLs, one being an improvement in device performance through a buried-heterostructure (BH) regrowth study, and the other being a realization of single-mode tunable QCLs integrated with distributed-Bragg-reflector (DBR) grating and thermal tuning mechanism.
Efficient heat dissipation in the QCL active region, which is crucial for high optical-power operation, can be effectively achieved using BH waveguides laterally embedded with InP grown by metal-organic chemical vapor disposition. We have experimentally studied the effects of the structural features of mesas, such as mesa orientation, geometry, sidewall-etched profile, and the length of the oxide overhang, on the BH regrowth. We find that the mesa oriented in the [01 1 ] direction with smoothly etched sidewalls produces a satisfactory planar growth profile and uniform lateral growth coverage and that a mesa-height–to–overhang-length ratio between 2.5 and 3.0 is effective in reducing anomalous growth in the vicinity of oxide edges. As a result, high-power QCLs capable of producing multi-hundred milliwatts at room temperature at ~4.6 μm and ~7.9 μm through reproducible BH regrowth results have been demonstrated.
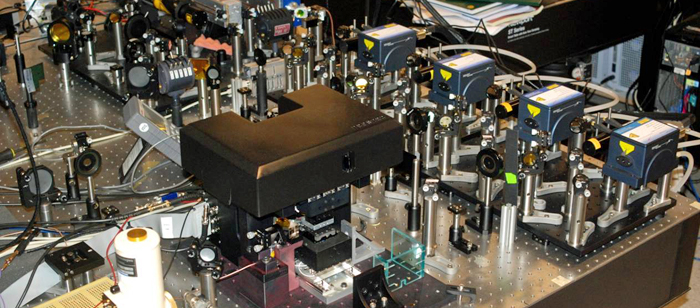
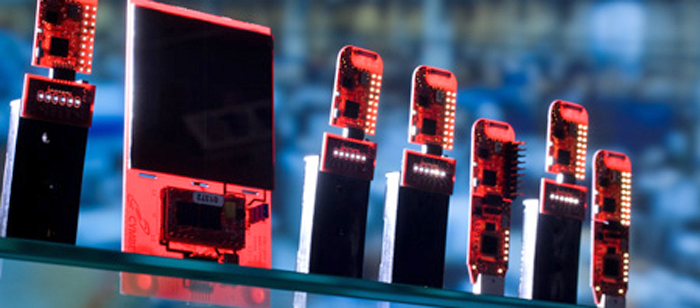
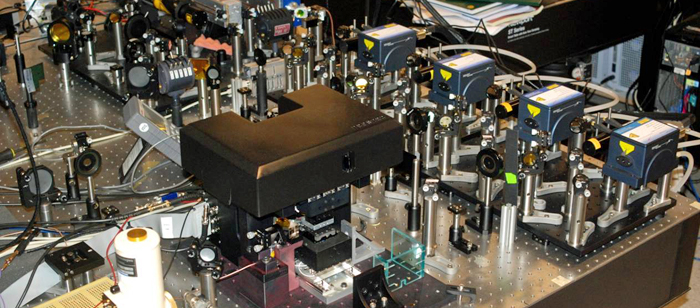
We have also demonstrated single-mode tunable QCLs operating at ~7.9 μm with an internal DBR grating structure and thermal tuning scheme incorporated. A special flip-chip bonding configuration and device assembly utilizing two copper heatsinks—one for the gain section and the other for the DBR grating section—were devised and constructed to achieve separate temperature controls in both sections. A miniature thermoelectric (TE) cooler dedicated to the DBR grating section was implemented to control the DBR grating temperature while the gain section was kept at a different temperature to achieve single-wavelength tuning. Under ±1000 mA bias conditions, a quasi-single-wavelength tuning range of ~7.2 cm-1 was realized across the TE cooler temperature span, combined with an additional temperature contrast of 56 °C between the two heatsinks (gain/DBR = 10/66 °C) owing to the implementation of additional temperature-controlling elements. We have also developed a two-dimensional thermal model to investigate the thermal dynamics in the device, including the temperature distribution and thermal dependency of each section, and the thermal response time, which ultimately dictates the wavelength tuning speed. We find that a 250-μm passive section located between the gain and DBR grating section can significantly improve temperature uniformity in both the sections as it absorbs most temperature gradients. Further, a swift thermal response time of ~7 ms is simulated if the DBR grating section is directly bonded on the miniature TE cooler.
More importantly, we have realized a monolithic photonic integration platform, both thermally and electrically, for mid-IR QCLs. The QCLs fabricated in this dissertation possess two major functionalities. The gain section, an active component, is electrically pumped to provide optical gain and is kept at a temperature different from the DBR grating section, and the DBR grating section, a passive component, provides optical feedback for single-wavelength emission and subsequently tunes the emission wavelength through a local temperature variation. Such thermal and optoelectronic integration opens new perspectives for mid-IR QC technology.
Committee: Drs. Fow-Sen Choa, Anthony Johnson, Li Yan, Ryan Robucci, Terrance Worchesky and Jocob Khurgin